Strong ES Model:::::: When Strong ES Model enabled, a system can not act as an IP router. And drops incoming IP packets with destination IP addresses that do not match the interface address. Outbound IP packets must use the interface address as the source IP address.
—————————————————————————————————————————–
SRP local compartment state can grep from the file::::::/var/opt/hpsrp/state/srpname
—————————————————————————————————————————–
To enable additional users for INIT compartment login:::::
>roleadm assign <usrname> SRPlogin-init
To enable additional groups for INIT compartment login::::::
>roleadm assign “&<group_name>” SRPlogin-init
—————————————————————————————————————————–
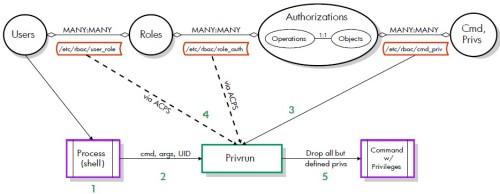
To allow additional users to use the srp_su command, following these steps::::::
- Create one new hpux.security.srp_su authorization per system:::authadm add hpux.security.srp_su
- Create a new role per SRP:::roleadm add newRole
- Assign the hpux.security.srp_su authorization to one role per SRP:::authadm assign newRole hpux.security.srp_su “srp_name”
- Assign a role to each user:::roleadm assign user_name newRole